Social engineering attacks are nothing new. In fact if you have a scary sounding intro you can suck a lot of unsuspecting people into downloading. This is particularly true when an attacker uses trademark images from well known security products like Norton and software companies like Adobe. Here is what this looks like. At the end are links to threat analysis from security vendors. It is a toolbar installer and browser hijacker. For the typical user what I mean to say is that clicking on this will probably run you $100+ if it ends up in the shop. Dont do it! -> [You can click the reduced images to actually read the text.]

The installer is even digitally signed with a certificate from Thawte. So much for the value in that extortion racket.
OK, so we know something. Now let’s run through the installer
Now the flash player is bogus. Now you get the chance to install the fabulous ClearThink popup and hijack engine. Herdprotect says:
“ClearThink is a brand of the Sambreel/Yontoo group, a web advertising company located in Carlsbad, CA. The company is a primary distributor of adware type software. It is part of the Yontoo/Sambreel group and distributes web browser add-ons, typically potentially unwanted and adware in nature, that are designed to modify a user’s typical search beahvior as well as display context and popup advertising.” Link
Forbes explained this outfit last year -> Forbes article 8-13-2013 Alex Konrad
Now it is time for yet another hijack called Astromenda. I will leave the description of this cyber grenade in the capable hands of Carine Febre
Now that you have been all jacked up, guess what’s next? You guessed it. A way to fix that.

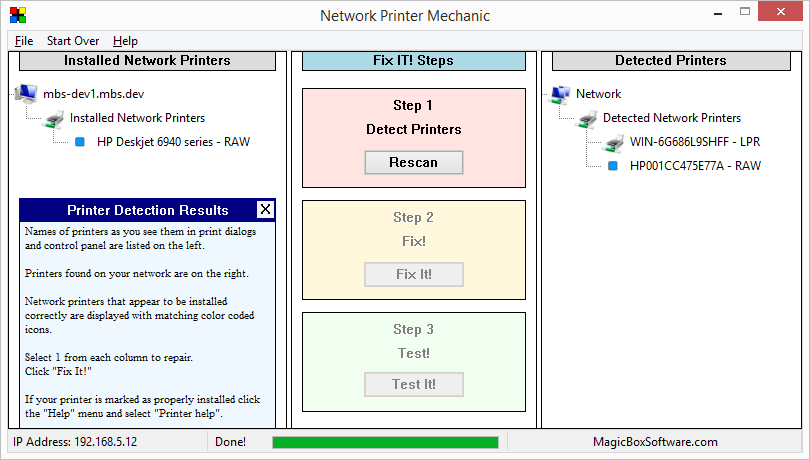
This will be the solution for some of the problems you will have by now. Scan is free. “Fix” is not.
You can read about this HERE
If all that good stuff was not enough, wait! There is more. DriverSupport!
You can read more about DriverSupport in this article by Ugnius Kiguolis
Now we have reached step 3.
Now for the grand finale! This is what you get when you click finish.
Now the deal is all of this stuff is bundled into a valueless installer. Even if any of these provide even a semblance of any value at any point that is far outweighed by the vandalism they leave behind on the unsuspecting.
Here is some additional information about the file -> http://www.herdprotect.com/adobe_flash_setup.exe-cf9f02bb022d961ab56666314fe61eb6eb9e9ffd.aspx
The code signing certificate serial is 37a48261fa2bd5edfe85e99767d8a6b8
Publisher Information Technology Systems – Podgorica, Montenegro
The distributor in the incident being documented is splendidsoft.net