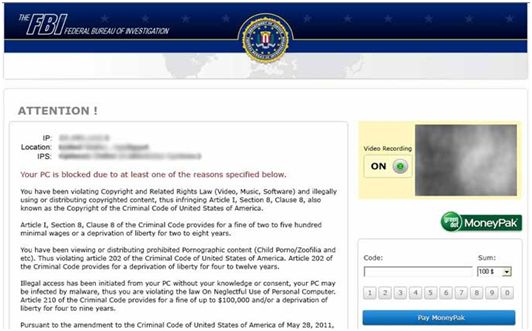
Fridays are never uneventful and this one was no exception. A call to the hotline indicates Reveton, aka Trojan:W32/Reveton, Win32/Reveton.A. What seemed interesting was that the user was savvy enough to get through the hijack, find and connect to my web site and subsequently to the remote client. This is a trivial removal at this point, so why is he calling me? Because there is very little honest “easy money” in this business and not a dime of it on Friday afternoon is why. The removal was straightforward enough, but nothing worked afterwards. I did notice evidence of at least one prior remote attempt.
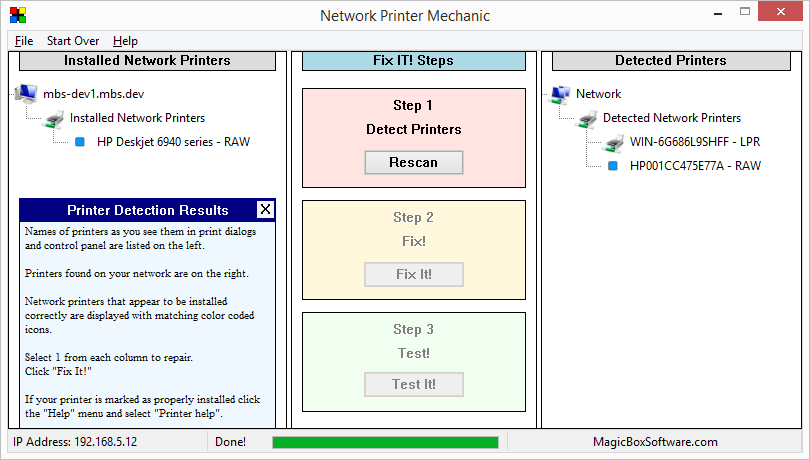
The firewall could not start because the registry key of a dependent service had been deleted, the firewall and antivirus notifications had been disabled and McAfee seemed unaware it was swimming neck deep in malware infested waters. As an added bonus we have a good selection of hidden files, from pictures and documents to a select group of shortcuts on the desktop. Among the other prizes were some nicely infected and corrupted restore points. That is why they call this stuff ransomware.
My advice is simple. You can send $200 to the FBI via MoneyPack or you can pay one of my associates $49.95 to put your system back in order. As always they never ask you to pay until you are satisfied with the work.
Here is a link to some information on the UK version of this sociopathic software. http://www.bleepingcomputer.com/virus-removal/remove-police-central-e-crime-unit-reveton-ransomware